How To Install Mail Server In Linux
Setting up your own email server on Linux from scratch is a pain in the butt, if you are not an advanced user. This tutorial will be showing you lot how to use iRedMail to quickly set upward a full-featured mail server on Ubuntu 18.04, saving you lots of fourth dimension and headaches.
What is iRedMail?
iRedMail is a trounce script that automatically installs and configures all necessary mail server components on your Linux/BSD server, thus eliminating manual installation and configuration. With iRedMail, you can easily create unlimited mailboxes and unlimited mail domains in a web-based admin panel. Mailboxes can be stored in MariaDB/MySQL, PostgreSQL database, or OpenLDAP. The following is a list of open-source software that volition be automatically installed and configured past iRedMail.
- Postfix SMTP server
- Dovecot IMAP server
- Nginx web server to serve the admin panel and webmail
- OpenLDAP, MySQL/MariaDB, or PostgreSQL for storing user data
- Amavised-new for DKIM signing and verification
- SpamAssassin for anti-spam
- ClamAV for anti-virus
- Roundcube webmail
- SOGo groupware, providing webmail, calendar (CalDAV), contacts (CardDAV), tasks and ActiveSync services.
- Fail2ban for protecting SSH
- mlmmj mailing listing director
- Netdata server monitoring
- iRedAPD Postfix policy server for greylisting
Step one: Choose the Right Hosting Provider and Buy a Domain Name
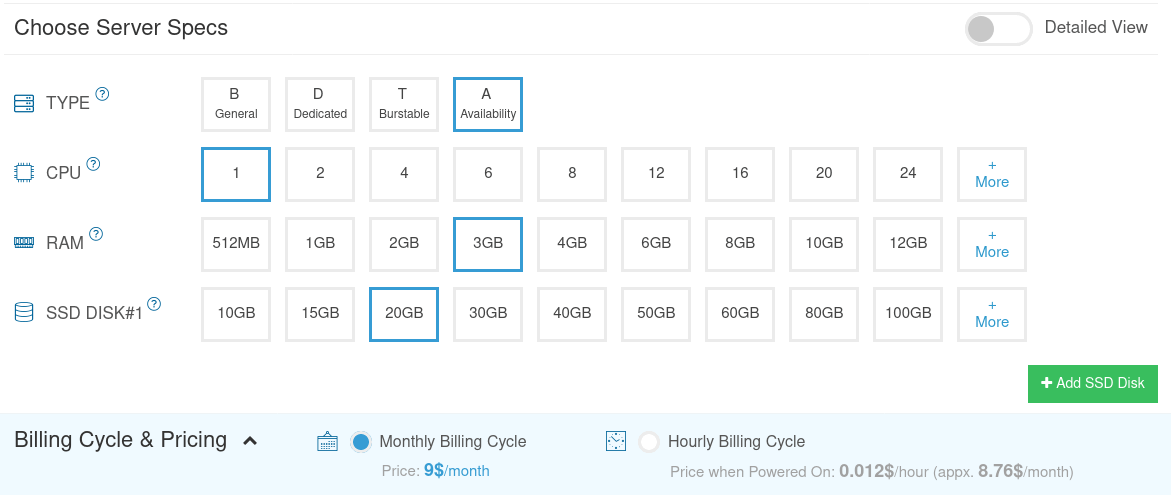
To gear up a total-featured email server with iRedMail, you need a server with at to the lowest degree 3GB RAM, because afterwards the installation, your server volition use more than than 2GB of RAM.
It is highly recommended that yous install iRedMail on a clean install of Ubuntu 18.04 server.
This tutorial is done on a $9/month Kamatera VPS (virtual individual server) with 1 CPU and 3GB RAM. They offering a 30-day complimentary trial.
Kamatera is a very expert selection to run a post server because
- They don't block port 25, so you can send unlimited emails (transactional email and newsletters) without spending money on SMTP relay service. Kamatera doesn't have any SMTP limits. Y'all can ship a million emails per day.
- The IP accost isn't on any electronic mail blacklist. (At to the lowest degree this is truthful in my instance. I chose the Dallas data center.) Yous definitely don't want to be listed on the dreaded Microsoft Outlook IP blacklist or the spamrats blacklist. Some blacklists block an entire IP range and you have no way to delist your IP address from this kind of blacklist.
- You can edit PTR tape to meliorate email deliverability.
- They let you to ship newsletters to your electronic mail subscribers with no hourly limits or daily limits, any.
- You can order multiple IP addresses for a single server. This is very useful for folks who need to ship a large book of emails. Yous can spread email traffic on multiple IP addresses to attain ameliorate email deliverability.
Other VPS providers like DigitalOcean blocks port 25. DigitalOcean would not unblock port 25, so you will demand to fix SMTP relay to featherbed blocking, which can cost you lot additional coin. If you utilise Vultr VPS, and so port 25 is blocked by default. They can unblock information technology if yous open a support ticket, simply they may cake information technology again at any fourth dimension if they decide your email sending activeness is non immune. Vultr actually may re-block information technology if you use their servers to transport newsletters.
Go to Kamatera website to create an account, and so create your server in your business relationship dashboard.
I recommend following the tutorial linked below to properly ready your Linux VPS server on Kamatera.
- How to Create a Linux VPS Server on Kamatera
One time y'all created a server, Kamatera volition transport you an email with the server SSH login details. To log into your server, you use an SSH customer. If you lot are using Linux or macOS on your computer, then but open up up a final window and run the following command to log into your server. Replace 12.34.56.78 with your server's IP accost.
ssh [email protected]
You will be asked to enter the password.
You as well need a domain proper name. I registered my domain name from NameCheap because the cost is low and they give whois privacy protection free for life.
Footstep two: Creating DNS MX Record
The MX tape specifies which host or hosts handle emails for a particular domain name. For example, the host that handles emails for linuxbabe.com is post.linuxbabe.com. If someone with a Gmail account sends an e-mail to [email protected], then Gmail server will query the MX tape of linuxbabe.com. When it finds out that postal service.linuxbabe.com is responsible for accepting email, it then query the A record of mail.linuxbabe.com to get the IP address, thus the email can be delivered.
In your DNS manager, create a MX tape for your domain name. Enter @ in the Name field to represent the principal domain proper name, and then enter mail.your-domain.com in the Value field.
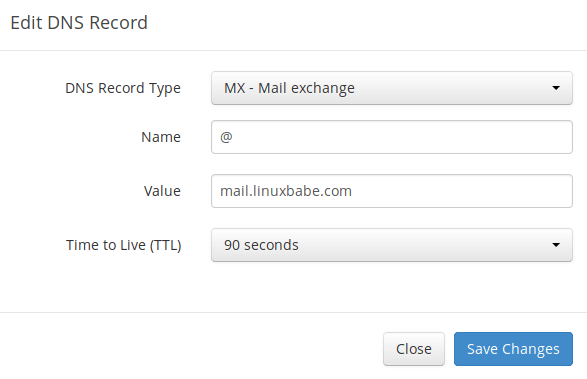
Note: The hostname for MX record can non be an alias to some other proper noun. Too, It's highly recommended that y'all use hostnames, rather than bare IP addresses for MX tape.
Your DNS managing director may require y'all to enter a preference value (aka priority value). It can be any number between 0 and 65,356. A small number has higher priority than a large number. It's recommended that yous set the value to 0, then this post server volition have the highest priority for receiving emails. After creating MX record, you lot also demand to create an A record for mail.your-domain.com , so that it tin be resolved to an IP address. If your server uses IPv6 address, be sure to add AAAA record.
Hint: If yous apply Cloudflare DNS service, you should not enable the CDN feature when creating A record for mail service.your-domain.com. Cloudflare does not support SMTP proxy.
Pace 3: Configuring Hostname
Log into your server via SSH, and then run the following command to update existing software packages.
sudo apt update sudo apt upgrade
I strongly recommend creating a sudo user for managing your server rather than using the default root user. Run the following command to create a user. Supplant username with your preferred username.
adduser username 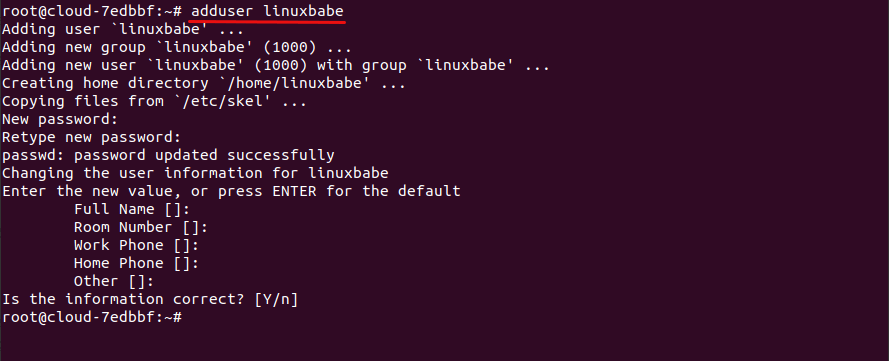
Then add the user to the sudo group.
adduser username sudo Then switch to the new user.
su - username Next, fix a fully qualified domain proper noun (FQDN) for your server with the following command.
sudo hostnamectl ready-hostname mail.your-domain.com We too demand to update /etc/hosts file with a control line text editor like Nano.
sudo nano /etc/hosts
Edit it similar below. (Use arrow keys to move the cursor in the file.)
127.0.0.1 mail service.your-domain.com localhost Save and close the file. (To save a file in Nano text editor, printing Ctrl+O, then printing Enter to ostend. To shut the file, press Ctrl+10.)
To encounter the changes, re-login and then run the following control to see your hostname.
hostname -f
Step four: Setting up Mail Server on Ubuntu eighteen.04 with iRedMail
Run the following commands to download the latest version of iRedMail script installer from its Github repository.
wget https://github.com/iredmail/iRedMail/archive/1.5.0.tar.gz
Extract the archived file.
tar xvf ane.v.0.tar.gz
Then cd into the newly-created directory.
cd iRedMail-1.v.0/
Add executable permission to the iRedMail.sh script.
chmod +x iRedMail.sh
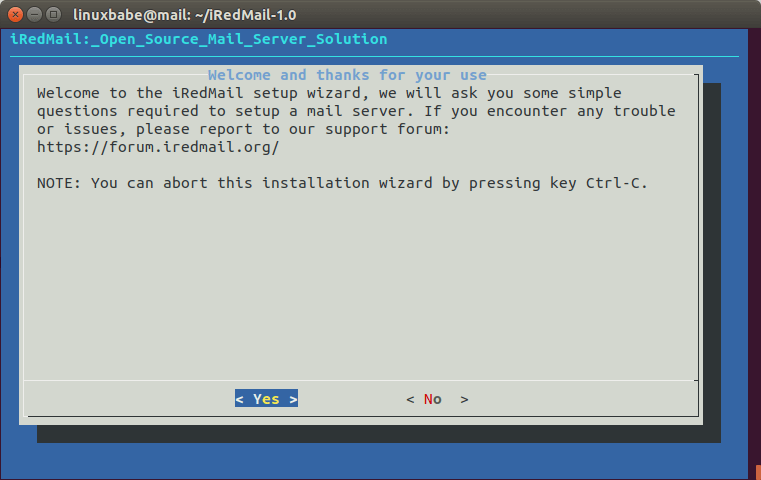
Adjacent, run the Fustigate script with sudo privilege.
sudo bash iRedMail.sh
The mail server setup magician volition appear. Use the Tab key to select Yes and press Enter.
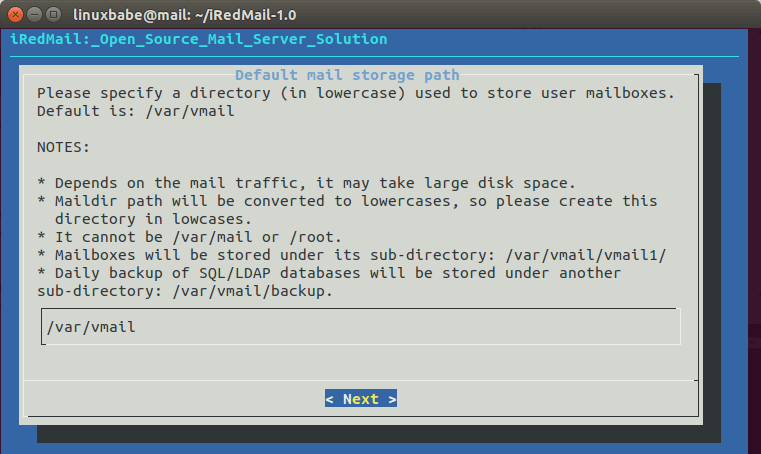
The next screen will ask y'all to select the mail storage path. You lot tin use the default one /var/vmail, so simply press Enter.
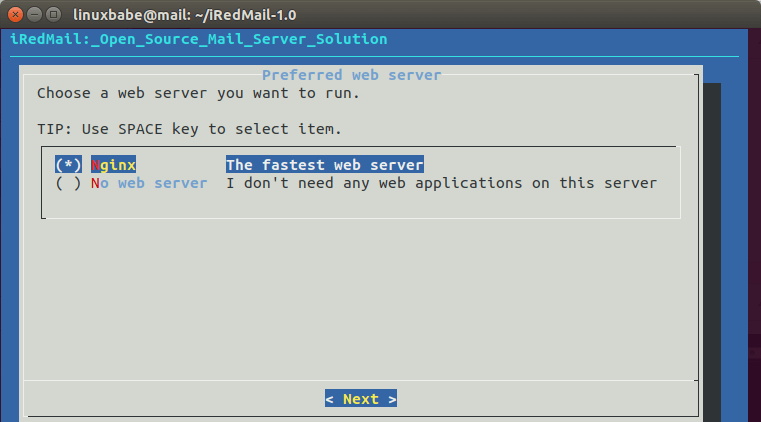
Then choose whether you want to run a web server. It's highly recommended that you cull to run a web server because you need the web-based admin panel to add email accounts. Too, it allows you to access the Roundcube webmail. Past default, Nginx web server is selected, so you can simply printing Enter. (An asterisk indicates the item is selected.)
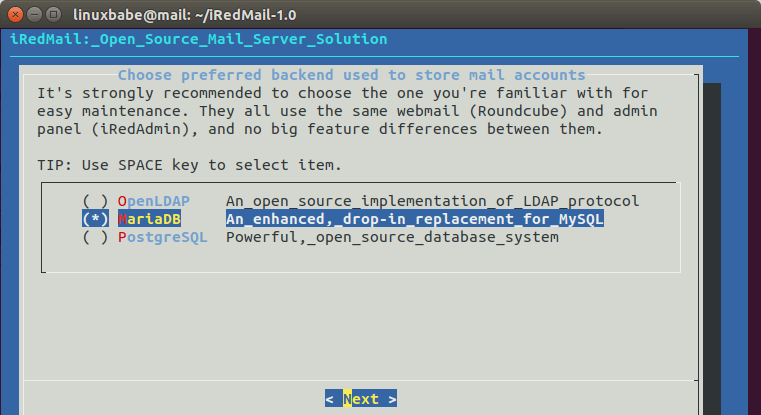
Then select the storage backend for email accounts. Cull one that y'all are familiar with. This tutorial chose MariaDB. Press up and down arrow key and press the space bar to select.
If y'all selected MariaDB or MySQL, then you lot volition demand to set the MySQL root password.
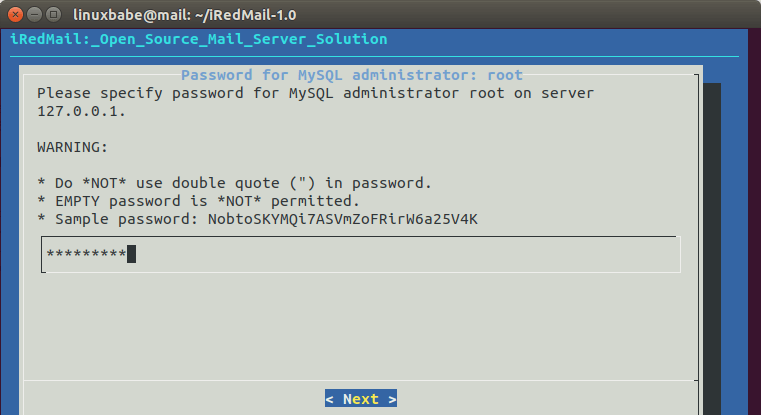
Note that if you selected MariaDB, then you don't need countersign to log into MariaDB shell. Instead of running the normal command mysql -u root -p, you can run the following command to login, with sudo and without providing MariaDB root countersign.
sudo mysql -u root
This is considering the MariaDB package on Ubuntu eighteen.04 uses unix_socket authentication plugin, which allows users to use OS credentials to connect to MariaDB, just you still demand to set root password in iRedMail setup wizard.
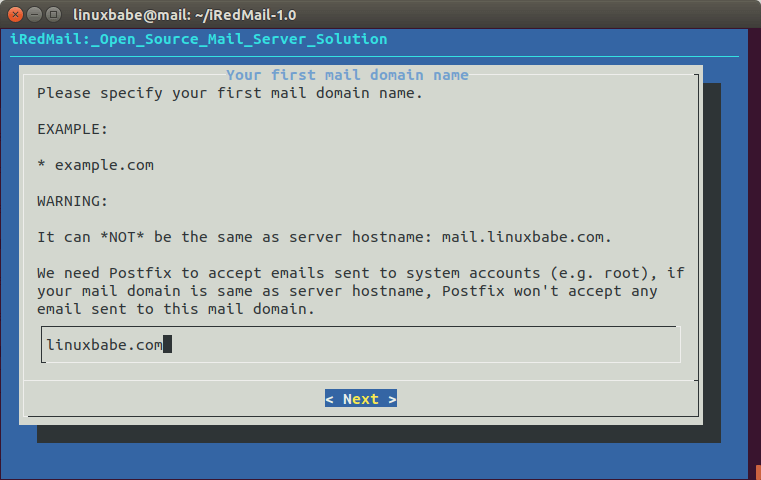
Next, enter your outset mail domain. Y'all can add together additional mail domains later in the web-based admin console. This tutorial assumes that yous want an email business relationship similar [email protected]. In that instance, you need to enter your-domain.com here, without sub-domain. Do not press the space bar later your domain proper name. I think iRedMail volition copy the space character along with your domain name, which can result in installation failure.
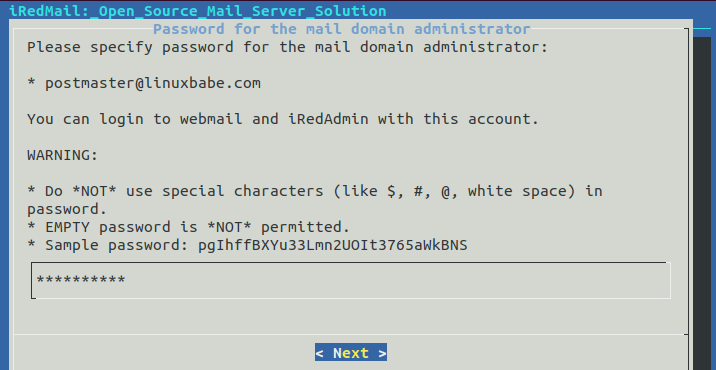
Adjacent, set a countersign for the mail domain administrator.
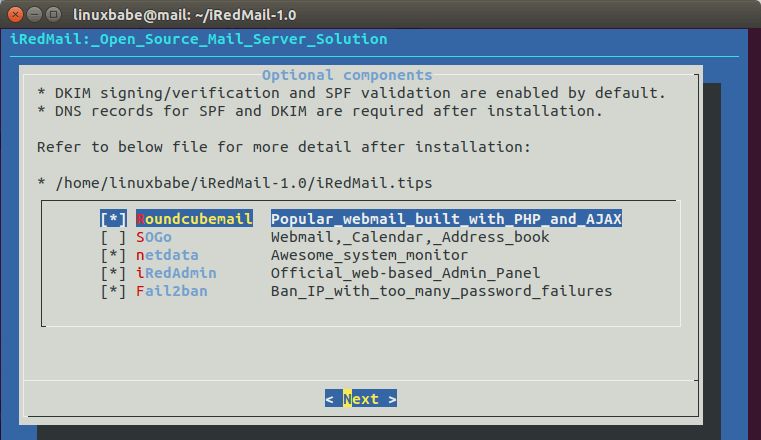
Choose optional components. By default, 4 items are selected. If you similar to accept SOGo groupware, then select information technology and press Enter.
Now you lot tin review your configurations. Type Y to begin the installation of all postal service server components.
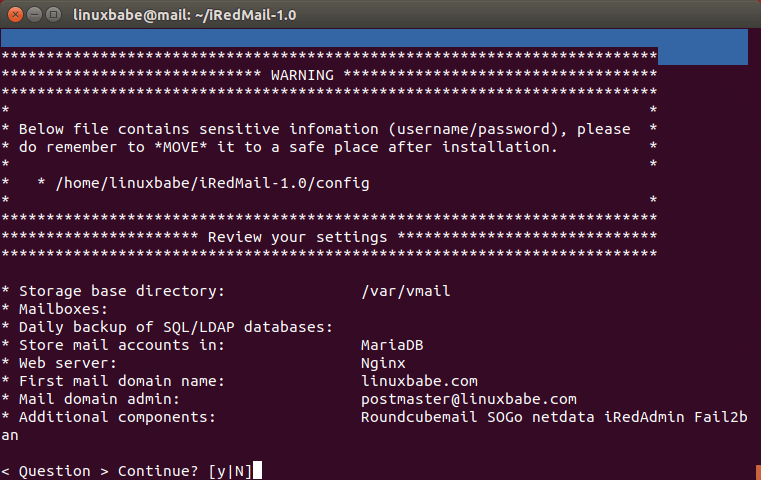
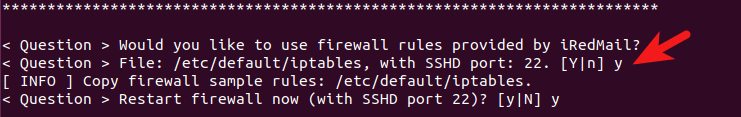
At the end of installation, choose y to use firewall rules provided past iRedMail and restart firewall.
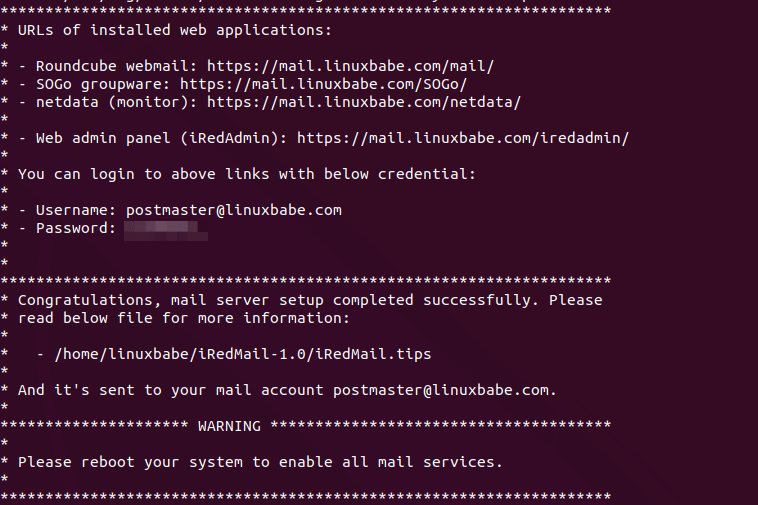
Now iRedMail installation is complete. You will be notified the URL of webmail, SOGo groupware and web admin panel and the login credentials. The iRedMail.tips file contains of import information about your iRedMail server.
Reboot your Ubuntu 18.04 server.
sudo shutdown -r now
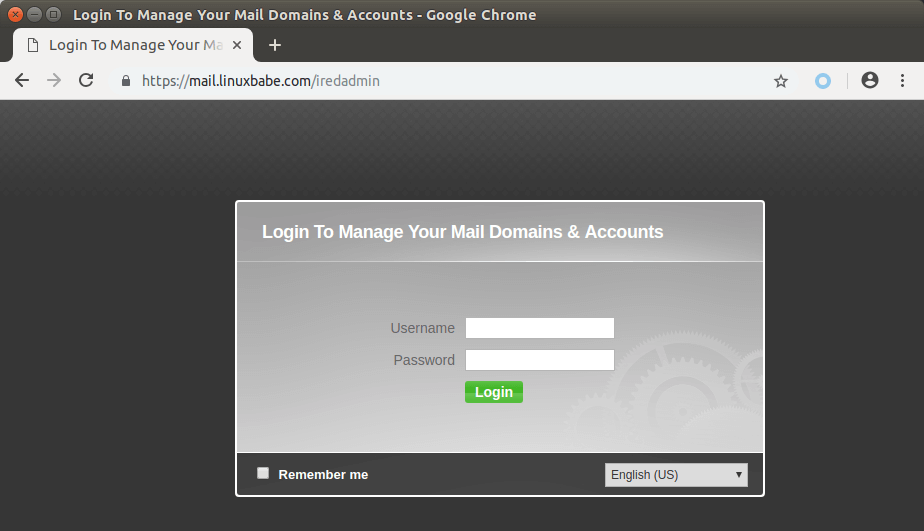
One time your server is back online, yous tin visit the spider web admin panel.
https://mail service.your-domain.com/iredadmin/
Annotation that in the above URL, the sub-directory for accessing the admin panel is /iredadmin/, not /iredmail/. And because it'due south using a cocky-signed TLS certificate, you demand to add security exception in your spider web browser.
Step 5: Installing Let's Encrypt TLS Certificate
Since the mail server is using a cocky-signed TLS certificate, both desktop post client users and webmail customer users volition see a warning. To set this, we can obtain and install a gratuitous Let'south Encrypt TLS certificate.
Obtaining the Certificate
Offset, log into your server again via SSH and run the following commands to install Permit's Encrypt (certbot) client on Ubuntu 18.04.
sudo apt install software-properties-common sudo add-apt-repository ppa:certbot/certbot -y sudo apt install certbot -y
iRedMail has already configured TLS settings in the default Nginx virtual host, and then here I recommend using the webroot plugin, instead of nginx plugin, to obtain certificate. Run the following control. Replace ruby-red text with your bodily information.
sudo certbot certonly --webroot --agree-tos --email [electronic mail protected] -d post.your-domain.com -w /var/world wide web/html/
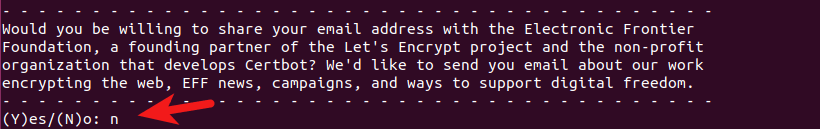
When information technology asks you if you desire to receive communications from EFF, you tin can cull No.
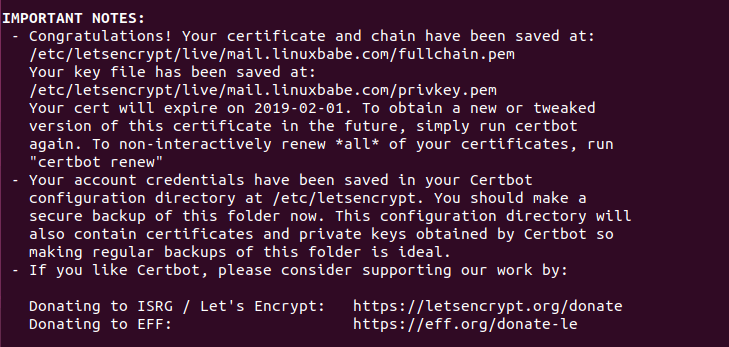
If everything went well, you will see the following text indicating that you accept successfully obtained a TLS certificate. Your document and chain have been saved at /etc/letsencrypt/live/mail.your-domain.com/ directory.
Failure to Obtain TLS Certificate
If certbot failed to obtain TLS certificate, perhaps information technology'south considering your DNS records are not propagated to the Cyberspace. Depending on the domain registrar you use, your DNS tape might be propagated instantly, or it might take upwards to 24 hours to propagate. Y'all can go to https://dnsmap.io, enter your postal service server's hostname (mail.your-domain.com) to bank check DNS propagation.
If certbot failed to obtain a certificate and you saw the following message,
Failed authorization procedure. mail.linuxbabe.com (http-01): urn:ietf:params:acme:error:connection :: The server could non connect to the customer to verify the domain :: Fetching https://mail.linuxbabe.com/.well-known/height-challenge/IZ7hMmRE4ZlGW7cXYoq2Lc_VrFzVFyfW6E0pzNlhiOA: Timeout during connect (probable firewall problem)
It might be that y'all have set AAAA record for mail.your-domain.com, just Nginx web server doesn't listen on IPv6 accost. To fix this error, edit the /etc/nginx/sites-enabled/00-default.conf file
sudo nano /etc/nginx/sites-enabled/00-default.conf
Find the following line.
#heed [::]:80;
Remove the # graphic symbol to enable IPv6 for this Nginx virtual host.
heed [::]:80;
Save and close the file. Then edit the SSL virtual host /etc/nginx/sites-enabled/00-default-ssl.conf.
sudo nano /etc/nginx/sites-enabled/00-default-ssl.conf
Add the post-obit line.
listen [::]:443 ssl http2;
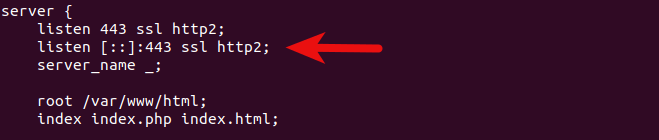
Save and shut the file. So test Nginx configuration.
sudo nginx -t
If the test is successful, reload Nginx for the change to take result.
sudo systemctl reload nginx
Run the following command again to obtain TLS certificate. Replace ruby-red text with your actual data.
sudo certbot certonly --webroot --agree-tos --email [email protected] -d mail.your-domain.com -w /var/world wide web/html/
At present you should be able to successfully obtain TLS certificate.
Installing the Certificate in Nginx
After obtaining a TLS certificate, permit's configure Nginx web server to apply it. Edit the SSL template file.
sudo nano /etc/nginx/templates/ssl.tmpl
Find the following 2 lines.
ssl_certificate /etc/ssl/certs/iRedMail.crt; ssl_certificate_key /etc/ssl/private/iRedMail.key;
Replace them with:
ssl_certificate /etc/letsencrypt/live/postal service.your-domain.com/fullchain.pem; ssl_certificate_key /etc/letsencrypt/live/mail.your-domain.com/privkey.pem;
Relieve and shut the file. Then test nginx configuration and reload.
sudo nginx -t sudo systemctl reload nginx
Visit iRedMail admin console once again, your web browser won't warn y'all any more because Nginx is now using a valid TLS document.
Installing TLS Certificate in Postfix and Dovecot
We also need to configure Postfix SMTP server and Dovecot IMAP server to use the Allow's Encrypt issued document so that desktop mail client won't display security warning. Edit the main configuration file of Postfix.
sudo nano /etc/postfix/main.cf
Discover the following three lines. (line 95, 96, 97).
smtpd_tls_key_file = /etc/ssl/private/iRedMail.key smtpd_tls_cert_file = /etc/ssl/certs/iRedMail.crt smtpd_tls_CAfile = /etc/ssl/certs/iRedMail.crt
Replace them with:
smtpd_tls_key_file = /etc/letsencrypt/live/mail.your-domain.com/privkey.pem smtpd_tls_cert_file = /etc/letsencrypt/alive/mail.your-domain.com/cert.pem smtpd_tls_CAfile = /etc/letsencrypt/live/mail.your-domain.com/chain.pem
Save and close the file. So reload Postfix.
sudo systemctl reload postfix
Side by side, edit the principal configuration file of Dovecot.
sudo nano /etc/dovecot/dovecot.conf
Fine the following 2 lines. (line 47, 48)
ssl_cert = </etc/ssl/certs/iRedMail.crt ssl_key = </etc/ssl/private/iRedMail.cardinal
Supersede them with:
ssl_cert = </etc/letsencrypt/live/mail.your-domain.com/fullchain.pem ssl_key = </etc/letsencrypt/live/mail service.your-domain.com/privkey.pem
Save and close the file. Then reload dovecot.
sudo systemctl reload dovecot
From now on, desktop mail service users won't see security warnings.
Stride 6: Sending Test Electronic mail
Log into iredadmin console with the postmaster mail service business relationship ([email protected]). In the Add together tab, you can add together boosted domains or email addresses.
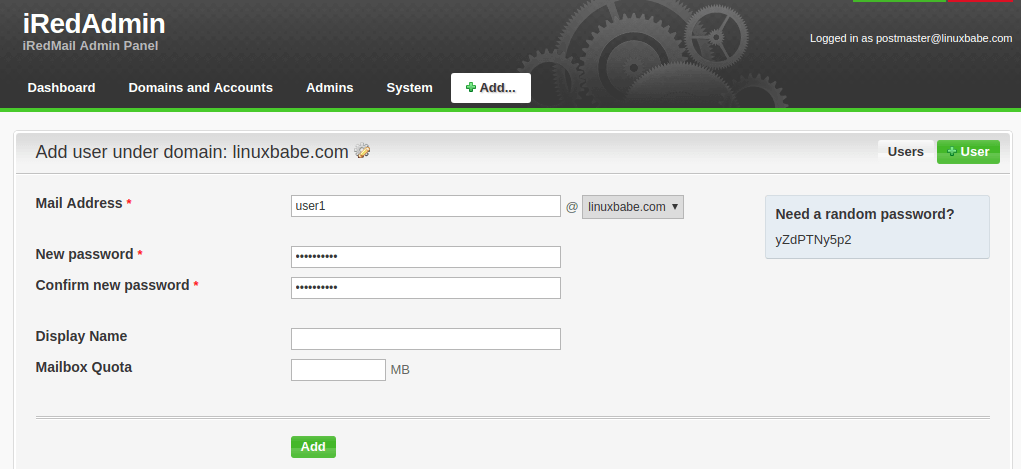
If you come across "no domain under control" mistake, please refer to this article.
After you create a user, you can visit the Roundcube webmail address and login with the new mail service user business relationship.
https://mail.your-domain.com/mail service/
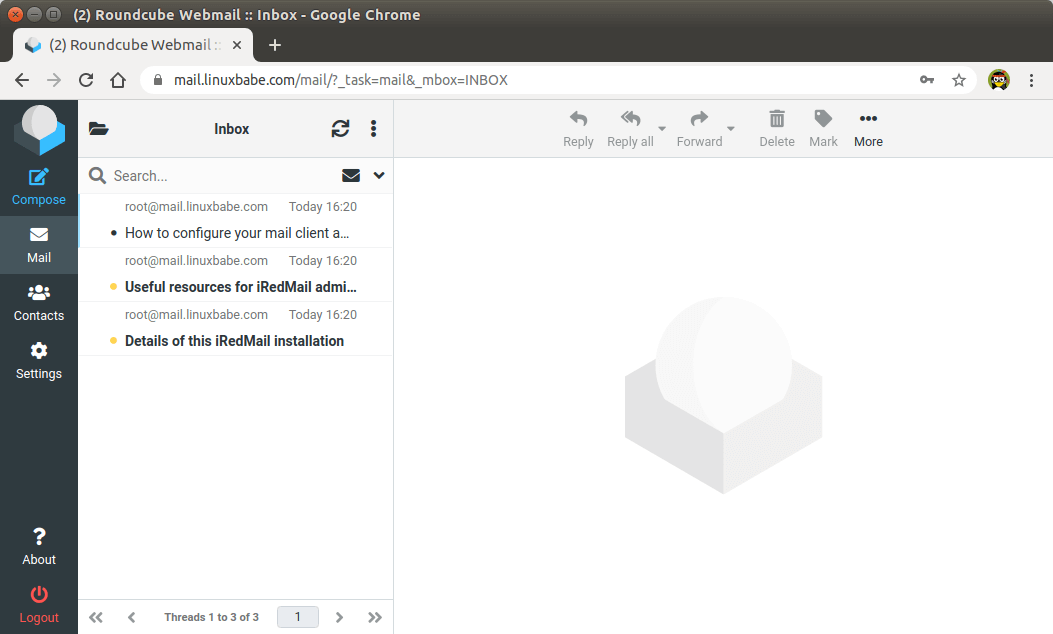
Now yous can test email sending and receiving. Please notation that yous may need to wait a few minutes to receive emails because iRedMail by default enables greylisting, which is a manner to tell other sending SMTP servers to try again in a few minutes. The following line in mail log file /var/log/mail.log indicates greylisting is enabled.
Recipient address rejected: Intentional policy rejection, please endeavor again later;
Calculation Swap Space
ClamAV is used to browse viruses in e-mail letters. ClamAV can use a fair amount of RAM. If in that location'southward not enough RAM on your server, ClamAV won't piece of work properly, which volition prevent your mail service server from sending emails. Y'all can add a swap file to your server to increase the total RAM on your server. (Note that using bandy infinite on the server volition degrade server operation. If you desire amend performance, yous should upgrade the physical RAM instead of using swap space.)
To add swap space on the server, start, use the fallocate control to create a file. For case, create a file named swapfile with 1G capacity in root file system:
sudo fallocate -l 1G /swapfile
So make sure only root can read and write to it.
sudo chmod 600 /swapfile
Format it to swap:
sudo mkswap /swapfile
Output:
Setting up swapspace version 1, size = 1024 MiB (1073737728 bytes) no label, UUID=0aab5886-4dfb-40d4-920d-fb1115c67433
Enable the swap file
sudo swapon /swapfile
To mount the swap space at arrangement kick time, edit the /etc/fstab file.
sudo nano /etc/fstab
Add together the following line at the bottom of this file.
/swapfile swap swap defaults 0 0
Save and close the file. So reload systemd and restart ClamAV.
sudo systemctl daemon-reload sudo systemctl restart clamav-daemon
Step 7: Checking If Port 25 (outbound) is blocked
Your ISP or hosting provider won't block incoming connectedness to port 25 of your server, which means you can receive emails from other mail servers. However, many ISP/hosting providers block outgoing connection to port 25 of other mail servers, which means you can't send emails.
If your electronic mail didn't arrive at your other email address such as Gmail, then run the post-obit control on your mail server to cheque if port 25 (outbound) is blocked.
telnet gmail-smtp-in.l.google.com 25
If it'due south not blocked, yous would come across messages like below, which indicates a connection is successfully established. (Hint: Type in quit and press Enter to close the connectedness.)
Trying 74.125.68.26... Continued to gmail-smtp-in.l.google.com. Escape character is '^]'. 220 mx.google.com ESMTP y22si1641751pll.208 - gsmtp
If port 25 (outbound) is blocked, you would meet something similar:
Trying 2607:f8b0:400e:c06::1a... Trying 74.125.195.27... telnet: Unable to connect to remote host: Connexion timed out
In this case, your Postfix can't transport emails to other SMTP servers. Ask your ISP/hosting provider to open it for y'all. If they refuse your asking, you need to gear up upwards SMTP relay to featherbed port 25 blocking.
Still Tin can't Ship Email?
If port 25 (outbound) is not blocked, but you lot still can't send emails from your ain mail server to your other electronic mail address similar Gmail, then you should cheque the post log (/var/log/mail service.log).
sudo nano /var/log/post.log
For example, some folks might see the following lines in the file.
host gmail-smtp-in.l.google.com[2404:6800:4003:c03::1b] said: 550-five.7.ane [2a0d:7c40:3000:b8b::2] Our system has detected that 550-5.7.1 this message does not run across IPv6 sending guidelines regarding PTR 550-five.7.1 records and authentication. Please review 550-five.vii.1 https://support.google.com/mail/?p=IPv6AuthError for more information
This means your mail server is using IPv6 to ship the email, but you didn't set IPv6 records. You should become to your DNS director, set AAAA record for mail.your-domain.com, then you lot should set up PTR tape for your IPv6 address, which is discussed in stride 9.
Step viii: Using Mail Clients on Your Computer or Mobile Device
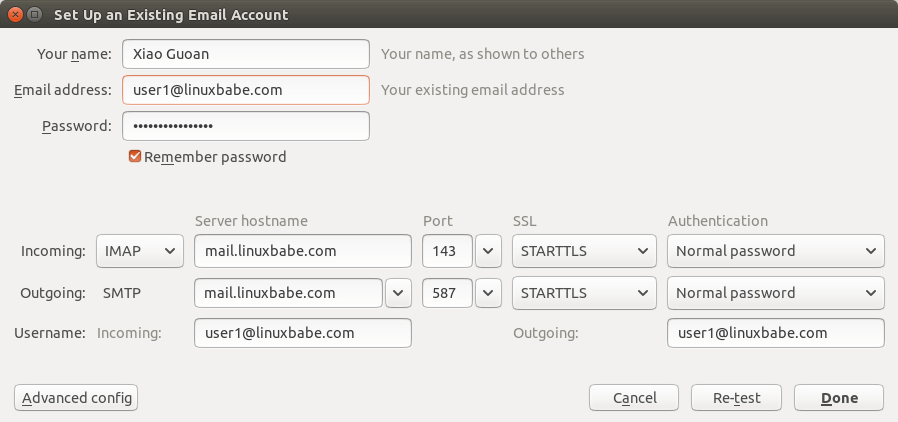
Fire upward your desktop e-mail client such as Mozilla Thunderbird and add a mail business relationship.
- In the incoming server section, select IMAP protocol, enter
mail.your-domain.comas the server name, choose port 143 and STARTTLS. Choosenormal passwordas the authentication method. - In the outgoing department, select SMTP protocol, enter
mail service.your-domain.comas the server name, choose port 587 and STARTTLS. Choosenormal passwordequally the authentication method.
Fail2ban Blocking Your Ain IP Address
If you made a mistake and failed to log in to mail server multiple times, then the Fail2ban service on the mail service server might block your IP accost. You can add together your IP address to whitelist by editing the jail.local file.
sudo nano /etc/fail2ban/jail.local
Add together your ain IP accost to the ignore list like below. Supervene upon 12.34.56.78 with your real IP address.
ignoreip = 12.34.56.78 127.0.0.1 127.0.0.0/8 10.0.0.0/8 172.16.0.0/12 192.168.0.0/16 Save and close the file. Then restart Fail2ban.
sudo systemctl restart fail2ban
Footstep 9: Improving Email Deliverablity
To preclude your emails from being flagged as spam, you should set PTR, SPF, DKIM and DMARC records.
PTR record
A pointer tape, or PTR record, maps an IP accost to a FQDN (fully qualified domain name). It's the analogue to the A tape and is used for reverse DNS lookup, which can assist with blocking spammers. Many SMTP servers reject emails if no PTR record is found for the sending server.
To cheque the PTR record for an IP address, run this command:
dig -x IP-address +brusque
or
host IP-address
PTR record isn't managed by your domain registrar. It'southward managed past the organization that gives y'all an IP accost. Because you get IP address from your hosting provider or Internet service provider, not from your domain registrar, so yous must set PTR record for your IP in the control panel of your hosting provider, or ask your Internet access provider. Its value should be your mail server'southward hostname: mail.your-domain.com. If your server uses IPv6 address, exist sure to add a PTR tape for your IPv6 accost as well.
To edit the reverse DNS tape for your Kamatera VPS, log into the Kamatera client surface area, then open a support ticket and tell them to add together PTR record for your server IP addresss to point the IP accost to mail.your-domain.com. It's not user-friendly, you might think, but this is to keep spammers away from the platform, so legitimate email senders like united states of america will have a great IP reputation.
SPF Record
SPF (Sender Policy Framework) tape specifies which hosts or IP accost are allowed to send emails on behalf of a domain. You should allow but your own email server or your Internet access provider'south server to transport emails for your domain. In your DNS management interface, create a new TXT record like below.
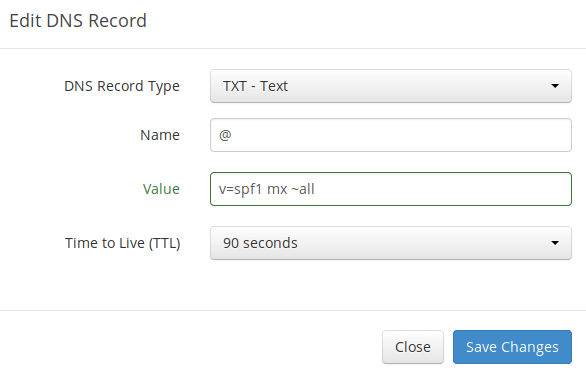
Explanation:
- TXT indicates this is a TXT record.
- Enter @ in the proper noun field to stand for the chief domain name.
- 5=spf1 indicates this is a SPF record and the version is SPF1.
- mx ways all hosts listed in the MX records are allowed to send emails for your domain and all other hosts are disallowed.
- ~all indicates that emails from your domain should only come up from hosts specified in the SPF record. Emails that are from other hosts will be flagged equally forged.
To bank check if your SPF tape is propagated to the public Cyberspace, you can use the dig utility on your Linux machine similar below:
dig your-domain.com txt
The txt option tells dig that we but want to query TXT records.
DKIM Record
DKIM (DomainKeys Identified Mail) uses a private central to digitally sign emails sent from your domain. Receiving SMTP servers verify the signature past using the public key, which is published in the DNS DKIM record.
The iRedMail script automatically configured DKIM for your server. The only matter left to do is creating DKIM record in DNS managing director. Run the following command to testify the DKIM public key.
sudo amavisd-new showkeys
The DKIM public central is in the parentheses.
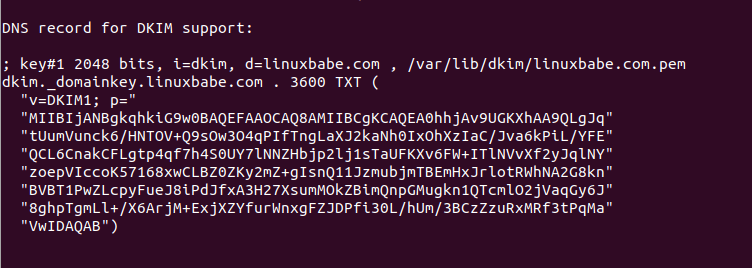
So in your DNS manager, create a TXT tape, enter dkim._domainkey in the name field. Copy everything in the parentheses and paste into the value field. Delete all double quotes and line breaks.
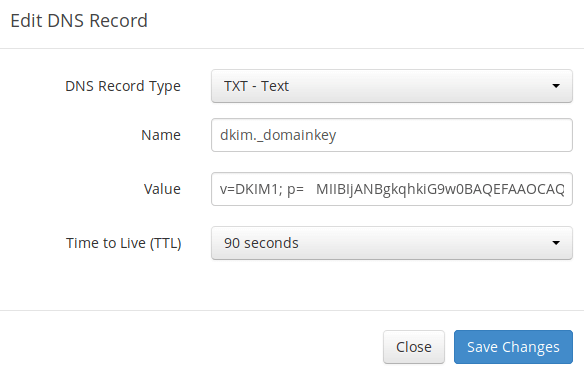
After saving your changes, run the following command to examination if your DKIM record is correct.
sudo amavisd-new testkeys
If the DKIM record is correct, the test volition laissez passer.
TESTING#1 linuxbabe.com: dkim._domainkey.linuxbabe.com => laissez passer
Annotation that your DKIM record may need sometime to propagate to the Internet. Depending on the domain registrar you utilise, your DNS record might exist propagated instantly, or it might take up to 24 hours to propagate. You can get to https://www.dmarcanalyzer.com/dkim/dkim-cheque/, enter dkim every bit the selector and enter your domain name to check DKIM record propagation.
DMARC Record
DMARC stands for Domain-based Bulletin Authentication, Reporting and Conformance. DMARC can help receiving email servers to identify legitimate emails and prevent your domain proper noun from existence used by email spoofing.
To create a DMARC record, go to your DNS managing director and add a TXT record. In the name field, enter _dmarc. In the value field, enter the following. (You should create the [email protected] email address.)
5=DMARC1; p=none; pct=100; rua=mailto:[electronic mail protected] 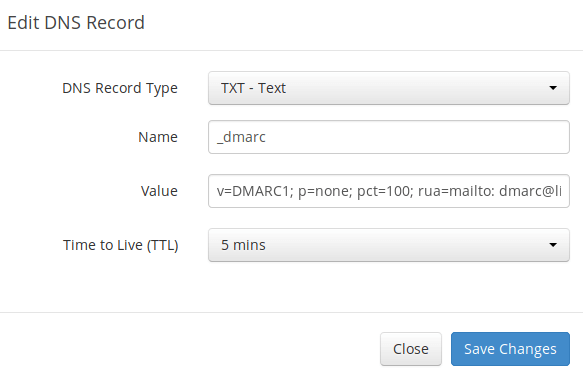
The higher up DMARC record is a safe starting signal. If you want to read the full explanation of DMARC, please check the following article. Note that this is optional.
- Creating DMARC Record to Protect Your Domain Proper noun From Email Spoofing
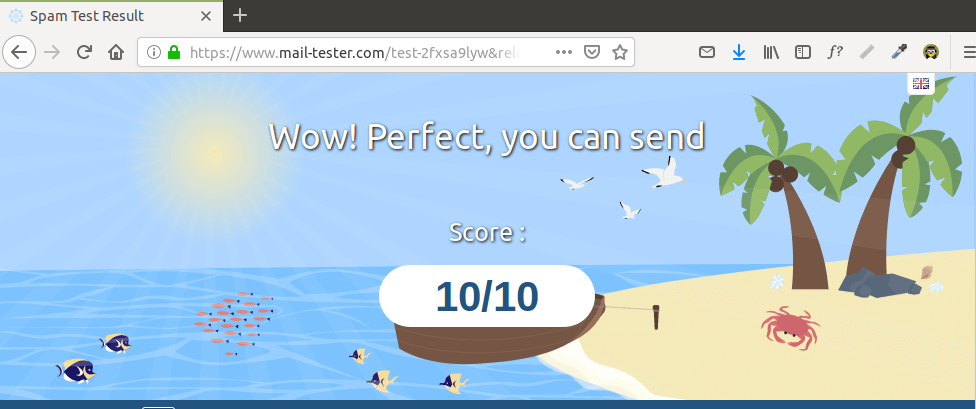
Step 10: Testing Electronic mail Score and Placement
Subsequently creating PTR, SPF, DKIM tape, become to https://www.mail service-tester.com. You will see a unique e-mail address. Send an email from your domain to this address and then check your score. As you tin can meet, I got a perfect score. In the examination consequence, you should bank check if your PTR tape, SPF and DKIM record is valid.
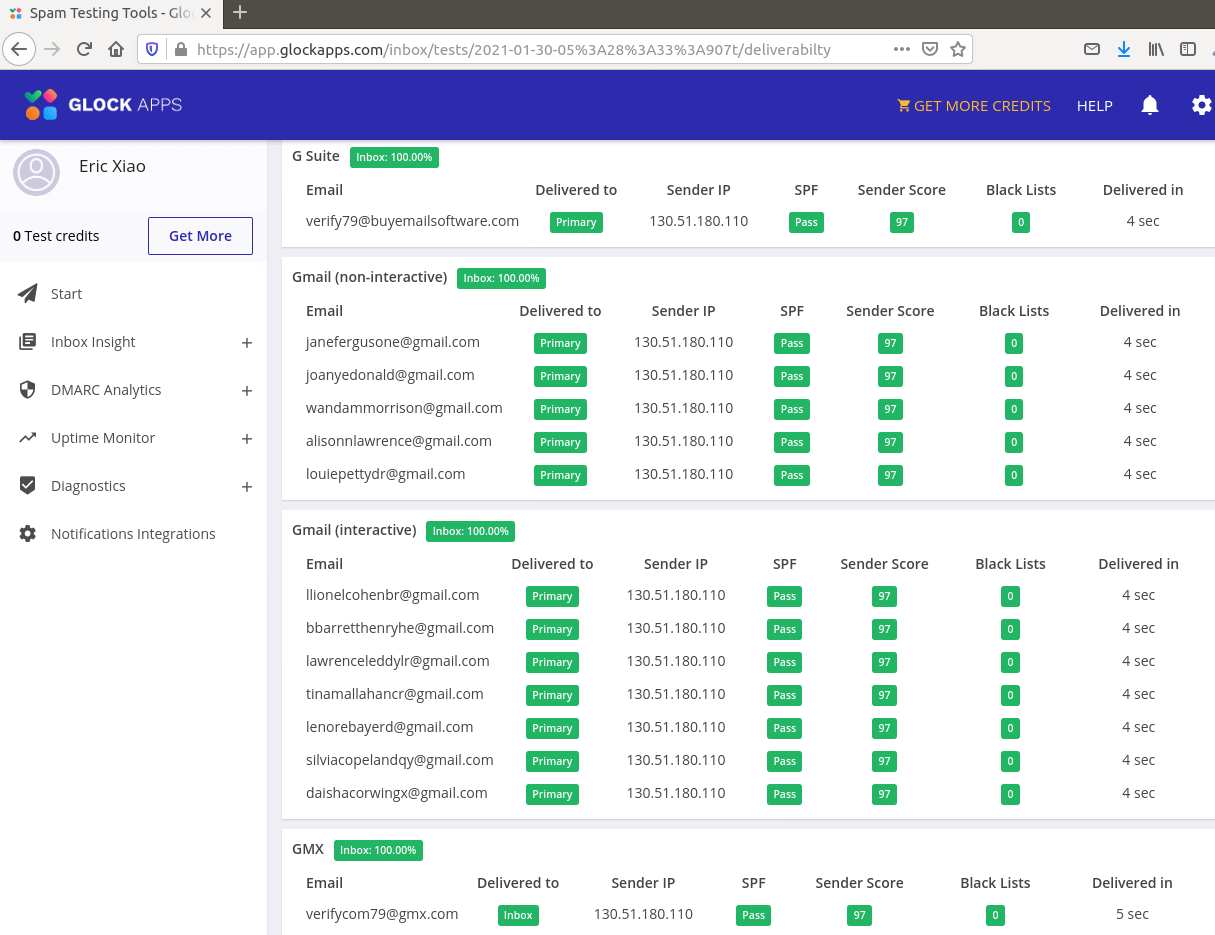
What if Your Emails Are All the same Existence Marked equally Spam?
I have more tips for you lot in this article: How to stop your emails being marked equally spam. Although information technology will have some time and effort, your emails will eventually exist placed in inbox afterwards applying these tips.
What if Your Email is Rejected by Microsoft Mailbox?
Microsoft seems to exist using an internal blacklist that blocks many legitimate IP addresses. If your emails are rejected by Outlook or Hotmail, you lot need to submit the sender information form. Afterwards that, your email will exist accepted by Outlook/Hotmail.
Calculation Multiple Mail Domains
I wrote this commodity to bear witness you how to add together multiple mail service domains in iRedMail.
How to Disable Greylisting
By default, iRedMail has enabled greylisting, which tells other sending SMTP servers to endeavour again in a few minutes. This is mainly useful to block spam, but it also degrades user experience. If you adopt to disable greylisting, follow the instructions below.
Add together write permission to the /opt/iredapd/settings.py file.
sudo chmod 600 /opt/iredapd/settings.py
And so edit the configuration file.
sudo nano /opt/iredapd/settings.py
Find the following line.
plugins = ["reject_null_sender", "wblist_rdns", "reject_sender_login_mismatch", "greylisting", "throttle", "amavisd_wblist", "sql_alias_access_policy"]
Remove "greylisting" from the list. Save and close the file. And so restart iredapd.
sudo systemctl restart iredapd
Change the configuration file back to read merely manner.
sudo chmod 400 /opt/iredapd/settings.py
Enabling SMTPS Port 465
If you are going to use Microsoft Outlook client, then you demand to enable SMTPS port 465 in Postfix SMTP server.
Troubleshooting Tips
Starting time, please use a VPS with at least 4GB RAM. Running iRedMail on a 1GB RAM VPS volition cause the database, SpamAssassin, or ClamAV to be killed because of out-of-retentivity problem. If you really want to use a 1GB RAM VPS, you are going to lose incoming emails and have other undesirable outcomes.
If the iRedMail web interface isn't attainable, like a 502 gateway error, y'all should bank check the Nginx logs in /var/log/nginx/ directory to discover clues.
If you can't transport or receive emails, check the mail log /var/log/mail.log.
Also, check if the diverse services are running.
systemctl status postfix systemctl status dovecot systemctl status nginx systemctl status mariadb systemctl status clamav-daemon systemctl status amavis
If you enabled the firewall, you should open up the post-obit ports in the firewall.
HTTP port: eighty HTTPS port: 443 SMTP port: 25 Submission port: 587 (and 465 if you are going to employ Microsoft Outlook mail client) IMAP port: 143 and 993
If you would similar to use the UFW firewall, check my guide here: Getting started with UFW firewall on Debian and Ubuntu.
How to Renew TLS Certificate
Let's Encrypt issued TLS certificate is valid for ninety days only and it'south important that y'all set up a Cron job to automatically renew the certificate. You can run the post-obit control to renew certificate.
sudo certbot renew -w /var/www/html
You can use the --dry-run pick to test the renewal process, instead of doing a real renewal.
sudo certbot renew -west /var/world wide web/html --dry-run
If you come across the following error when renewing TLS certificate.
The client lacks sufficient authorization :: Invalid response
So y'all demand to create the hidden directory.
sudo mkdir -p /var/www/html/.well-known/acme-challenge
And ready www-data as the owner of the webroot.
sudo chown www-data:www-data /var/www/html/ -R
As well, edit the SSL virtual host /etc/nginx/sites-enabled/00-default-ssl.conf. Add together the post-obit lines.
location ~ /.well-known/acme-claiming { root /var/www/html/; allow all; } 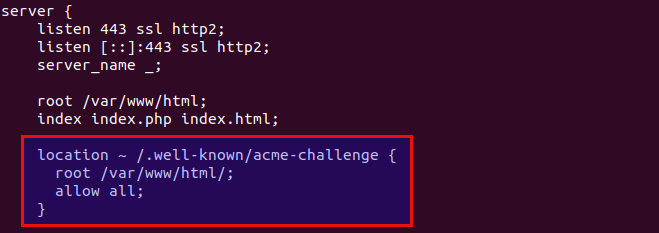
Salvage and close the file. Exam Nginx configuration and reload.
sudo nginx -t sudo systemctl reload nginx
Create Cron Chore
If now the dry run is successful, you can create Cron job to automatically renew certificate. But open root user's crontab file.
sudo crontab -e
Then add together the following line at the lesser of the file.
@daily certbot renew -west /var/www/html --quiet && systemctl reload postfix dovecot nginx
Reloading Postfix, Dovecot and Nginx is necessary to brand these programs pick upwardly the new certificate and private key.
Setting Upwards Backup Mail Server
Your primary mail server could be downward sometimes. If you host your mail server in a information center, and then the downtime is very minimal, and then y'all shouldn't be worried about losing inbound emails. If you lot host your mail server at home, the downtime can't be predicted and so it's a adept practice for y'all to run a backup post server in a data middle to preclude losing inbound emails. The fill-in post server needs but 512MB RAM to run. Please check the full detail in the following article.
- How to Prepare a Fill-in E-mail Server with Postfix on Ubuntu (Consummate Guide)
For Advanced Users
iRedMail doesn't include a DMARC verification service, you lot tin can check out the following tutorial to set upward OpenDMARC to block electronic mail spoofing.
- Set Up OpenDMARC with Postfix on Ubuntu to Block Email Spoofing/Spam
You may desire to customize the SpamAssassin content filter to better discover spam.
- Block Email Spam By Checking Header and Body in Postfix/SpamAssassin
If your website and mail service server are running on two unlike VPS (virtual individual server), you can prepare SMTP relay between your website and mail server, so that your website tin can ship emails through your post server. Come across the following commodity.
- How to ready SMTP relay between two Postfix SMTP servers on Ubuntu
Wrapping Up
That'south it! I hope this tutorial helped yous fix upward a mail server on Ubuntu 18.04 with iRedMail. Every bit always, if yous found this mail service useful, and then subscribe to our gratuitous newsletter to get more than tips and tricks. Take care 🙂
Source: https://www.linuxbabe.com/mail-server/ubuntu-18-04-iredmail-email-server
Posted by: gamblewhice1988.blogspot.com


0 Response to "How To Install Mail Server In Linux"
Post a Comment